IPsec(IP Security)是IETF制定的三层隧道加密协议,它为Internet上传输的数据提供了高质量的、可互操作的、基于密码学的安全保证。IPsec协议不是一个单独的协议,它给出了应用于IP层上网络数据安全的一整套体系结构,包括网络认证协议AH(Authentication Header,认证头)、ESP(Encapsulating Security Payload,封装安全载荷)和密钥管理协议IKE(Internet Key Exchange,因特网密钥交换)以及用于网络认证及加密的一些算法等。其中,AH协议和ESP协议用于提供安全服务,IKE协议用于密钥交换
IPsec VPN配置过程
- 定义感兴趣流
- 配置IKE安全提议
- 配置IKE对等体
- 配置IPsec安全提议
- 配置IKE方式的IPSec安全策略
- 调用到接口下
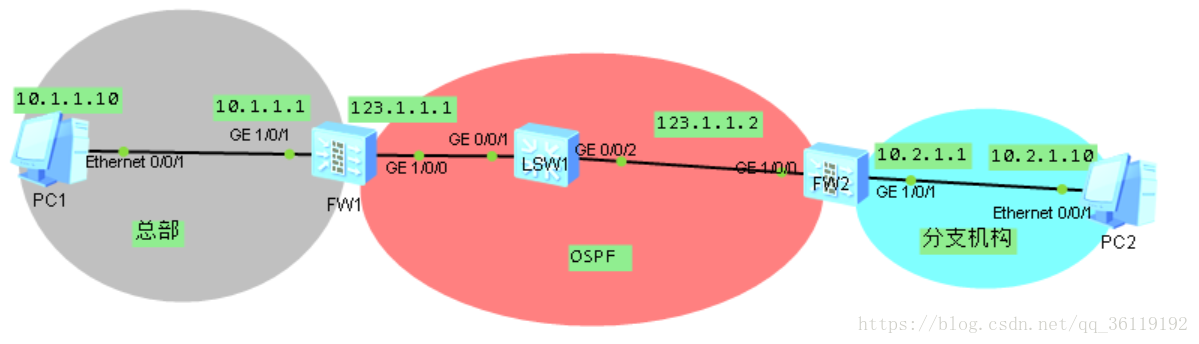
一:点对点的IPSec VPN
如图PC1是总部,PC2是分支机构,FW1、FW2是边界防火墙,他们之间建立IPSec VPN隧道(网关到网关,传输模式是tunnel)。他们之间运行ospf协议。现在要求PC1、PC2之间通过Ipsev VPN通信
PC1
PC>ipconfig
IPv4 address......................: 10.1.1.10
Subnet mask.......................: 255.255.255.0
Gateway...........................: 10.1.1.1
Physical address..................: 54-89-98-00-6F-A0PC2
PC>ipconfig
IPv4 address......................: 10.2.1.10
Subnet mask.......................: 255.255.255.0
Gateway...........................: 10.2.1.1
Physical address..................: 54-89-98-30-75-43FW1
[FW1]display current-configuration
#
acl number 3000 //第1步 匹配感兴趣流
rule 5 permit ip source 10.1.1.0 0.0.0.255 destination 10.2.1.0 0.0.0.255
#
ipsec proposal IPSEC_PROPOSAL //第4步 定义Ipsec安全提议
esp authentication-algorithm sha2-256
esp encryption-algorithm aes-256
#
ike proposal 10 // 第2步 配置ike安全提议
encryption-algorithm aes-256
dh group2
authentication-algorithm sha2-256
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256
#
ike peer IKE_PEER //第3步 配置ike对等体
undo version 2
pre-shared-key %@%@jL(M.m1SqQhN/QJv=zRP<C63%@%@
ike-proposal 10
remote-address 123.1.1.2
#
ipsec policy POLICY 1 isakmp // 第5步 配置IKE方式的IPsec安全策略
security acl 3000
ike-peer IKE_PEER
proposal IPSEC_PROPOSAL
#
interface GigabitEthernet1/0/0
undo shutdown
ip address 123.1.1.1 255.255.255.0
ipsec policy POLICY // 第6步 调用到该接口下
#
interface GigabitEthernet1/0/1
undo shutdown
ip address 10.1.1.1 255.255.255.0
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/1
#
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
#
ospf 100 router-id 11.1.1.1
import-route direct
area 0.0.0.0
network 123.1.1.1 0.0.0.0
#
security-policy
rule name LOCAL_TO_UNTRUST
source-zone local
source-zone untrust
destination-zone local
destination-zone untrust
service protocol 50
service protocol udp source-port 500 destination-port 500
service protocol 89
action permit
rule name TRUST_TO_UNTRUST
source-zone trust
source-zone untrust
destination-zone trust
destination-zone untrust
service icmp
action permit
# FW2
[FW2]display current-configuration
acl number 3000
rule 5 permit ip source 10.2.1.0 0.0.0.255 destination 10.1.1.0 0.0.0.255
#
ipsec proposal IPSEC_PROPOSAL
esp authentication-algorithm sha2-256
esp encryption-algorithm aes-256
#
ike proposal 10
encryption-algorithm aes-256
dh group2
authentication-algorithm sha2-256
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256
#
ike peer IKE_PEER
undo version 2
pre-shared-key %@%@q#!DL|f=v-#k:u,@q5w:fKR#%@%@
ike-proposal 10
remote-address 123.1.1.1
#
ipsec policy POLICY 1 isakmp
security acl 3000
ike-peer IKE_PEER
proposal IPSEC_PROPOSAL
#
interface GigabitEthernet1/0/0
undo shutdown
ip address 123.1.1.2 255.255.255.0
ipsec policy POLICY
#
interface GigabitEthernet1/0/1
undo shutdown
ip address 10.2.1.1 255.255.255.0
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/1
#
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
#
ospf 100 router-id 22.2.2.2
import-route direct
area 0.0.0.0
network 123.1.1.2 0.0.0.0
#
security-policy
rule name LOCAL_TO_UNTRUST
source-zone local
source-zone untrust
destination-zone local
destination-zone untrust
service protocol 50
service protocol udp source-port 500 destination-port 500
service protocol 89
action permit
rule name TRUST_TO_UNTRUST
source-zone trust
source-zone untrust
destination-zone trust
destination-zone untrust
service icmp
action permit
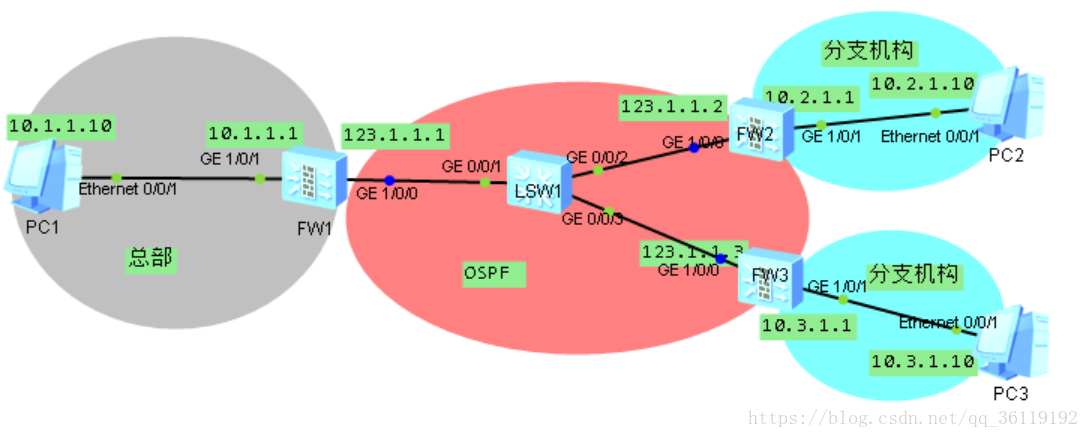
# 二:核心到分支的IPsec VPN,各核心之间也要能相互建立IPsec VPN
如图PC1是总部,PC2,PC3是分支机构,FW1、FW2、FW3是边界防火墙,他们之间建立IPSec VPN隧道。他们之间运行ospf协议。现在要求PC1、PC2、PC3之间通过Ipsev VPN隧道两两互通
核心到多分支和点到点的不同之处在于,第三步配置IKE对等体的时候总部不用配置 remote-address,第五步配置IPsec安全策略的时候先定义一个策略模板policy-template ,再调用到Ipsec安全策略下
PC1
PC>ipconfig
IPv4 address......................: 10.1.1.10
Subnet mask.......................: 255.255.255.0
Gateway...........................: 10.1.1.1
Physical address..................: 54-89-98-00-6F-A0
PC2
PC>ipconfig
IPv4 address......................: 10.2.1.10
Subnet mask.......................: 255.255.255.0
Gateway...........................: 10.2.1.1
Physical address..................: 54-89-98-30-75-43
PC3
PC>ipconfig
IPv4 address......................: 10.2.1.10
Subnet mask.......................: 255.255.255.0
Gateway...........................: 10.2.1.1
Physical address..................: 54-89-98-30-75-43FW1
[FW1]display current-configuration
#
acl number 3000
rule 5 permit ip destination 10.2.1.0 0.0.0.255
rule 10 permit ip destination 10.3.1.0 0.0.0.255
#
ipsec proposal IPSEC_PRO_CORE
esp authentication-algorithm sha2-256
esp encryption-algorithm aes-256
#
ike proposal 10
encryption-algorithm aes-256
dh group2
authentication-algorithm sha2-256
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256
#
ike peer IKE_PEER_CORE
undo version 2
pre-shared-key %@%@mZ,qW>TD+%Yh}1>SdS1L+I]p%@%@
ike-proposal 10
#
ipsec policy-template TEMP 1 //定义IPsec策略模板
security acl 3000
ike-peer IKE_PEER_CORE
proposal IPSEC_PRO_CORE
#
ipsec policy POLICY_CORE 1 isakmp template TEMP //调用该模板
#interface GigabitEthernet1/0/0
undo shutdown
ip address 123.1.1.1 255.255.255.0
ipsec policy POLICY_CORE
#
interface GigabitEthernet1/0/1
undo shutdown
ip address 10.1.1.1 255.255.255.0
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/1
#
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
#
ospf 100 router-id 11.1.1.1
import-route direct
area 0.0.0.0
network 123.1.1.1 0.0.0.0
#
security-policy
rule name LOCAL_TO_UNTRUST
source-zone local
source-zone untrust
destination-zone local
destination-zone untrust
service protocol 50 //ESP协议号
service protocol udp source-port 500 destination-port 500
service protocol 89 // OSPF协议号
action permit
rule name TRUST_TO_UNTRUST
source-zone trust
source-zone untrust
destination-zone trust
destination-zone untrust
service icmp
action permit
#FW2
[FW2]display current-configuration
acl number 3000
rule 5 permit ip source 10.2.1.0 0.0.0.255
#
ipsec proposal IPSEC_PROPOSAL
esp authentication-algorithm sha2-256
esp encryption-algorithm aes-256
#
ike proposal 10
encryption-algorithm aes-256
dh group2
authentication-algorithm sha2-256
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256
#
ike peer IKE_PEER
undo version 2
pre-shared-key %@%@q#!DL|f=v-#k:u,@q5w:fKR#%@%@
ike-proposal 10
remote-address 123.1.1.1
#
ipsec policy POLICY 1 isakmp
security acl 3000
ike-peer IKE_PEER
proposal IPSEC_PROPOSAL
#
interface GigabitEthernet1/0/0
undo shutdown
ip address 123.1.1.2 255.255.255.0
ipsec policy POLICY
#
interface GigabitEthernet1/0/1
undo shutdown
ip address 10.2.1.1 255.255.255.0
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/1
#
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
#
ospf 100 router-id 22.2.2.2
import-route direct
area 0.0.0.0
network 123.1.1.2 0.0.0.0
#
security-policy
rule name LOCAL_TO_UNTRUST
source-zone local
source-zone untrust
destination-zone local
destination-zone untrust
service protocol 50
service protocol udp source-port 500 destination-port 500
service protocol 89
action permit
rule name TRUST_TO_UNTRUST
source-zone trust
source-zone untrust
destination-zone trust
destination-zone untrust
service icmp
action permit
#
FW3
[FW3]display current-configuration
#
acl number 3000
rule 5 permit ip source 10.3.1.0 0.0.0.255
#
ipsec proposal IPSEC_PROPOSAL
esp authentication-algorithm sha2-256
esp encryption-algorithm aes-256
#
ike proposal 10
encryption-algorithm aes-256
dh group2
authentication-algorithm sha2-256
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256
#
ike peer IKE_PEER
undo version 2
pre-shared-key %@%@nr&Z6&'lXV{>xj88rL~J1k(W%@%@
ike-proposal 10
remote-address 123.1.1.1
#
ipsec policy POLICY 1 isakmp
security acl 3000
ike-peer IKE_PEER
proposal IPSEC_PROPOSAL
#
interface GigabitEthernet1/0/0
undo shutdown
ip address 123.1.1.3 255.255.255.0
ipsec policy POLICY
#
interface GigabitEthernet1/0/1
undo shutdown
ip address 10.3.1.1 255.255.255.0
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/1
#
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
#
ospf 100 router-id 33.3.3.3
import-route direct
area 0.0.0.0
network 123.1.1.3 0.0.0.0
#
security-policy
rule name LOCAL_TO_UNTRUST
source-zone local
source-zone untrust
destination-zone local
destination-zone untrust
service protocol 50
service protocol udp source-port 500 destination-port 500
service protocol 89
action permit
rule name TRUST_TO_UNTRUST
source-zone trust
source-zone untrust
destination-zone trust
destination-zone untrust
service icmp
action permit
#