一.salt-自定义模块
1.在master端(server1)创建目录:
[root@server1 ~]# mkdir /srv/salt/_modules
2.在该目录下编辑disk的python模块
cd /srv/salt/_modules/
[root@server1 _modules]# vim my_disk.py
#! /usr/bin/env python
def df():
return __salt__['cmd.run']('df -h')
3.给server2推送测试:salt server2 saltutil.sync_modules
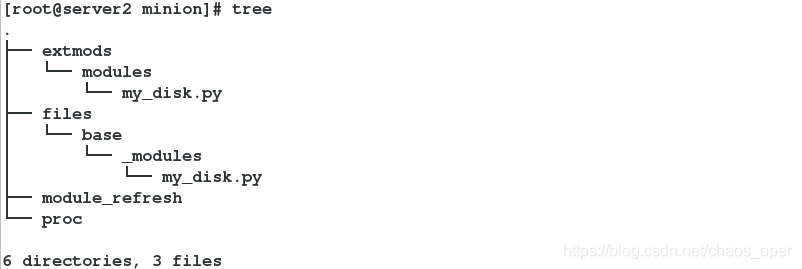
4. 在server2上,查看 /var/cache/salt/minion/目录结构
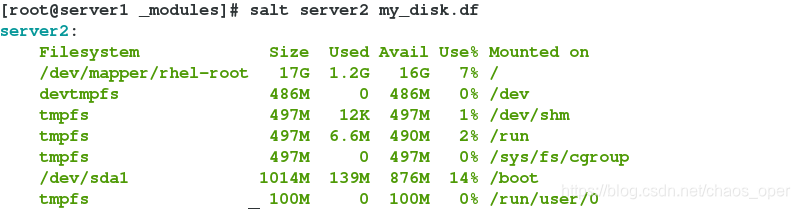
5.测试:salt server2 my_disk.df
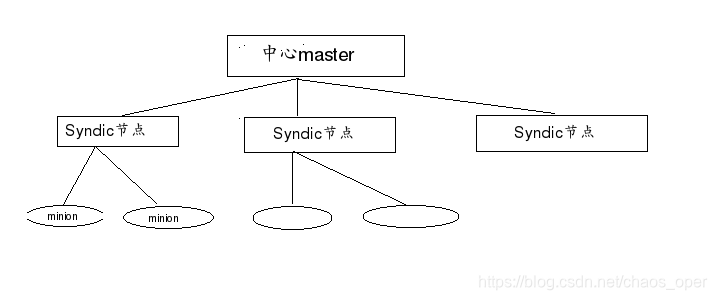
二.salt-syndic
中心master可以理解为公司大boss,syndic节点相当于公司经理,minion相当于是小员工。中心master将任务通过sysndic节点分发给minion端。
实验环境:
| 主机名 | 功能 |
|---|---|
| server1 | Syndic节点 |
| server2 | minion |
| server3 | minion |
| server4 | top master |
1.在server1上安装syndic: yum install -y salt-syndic
2.修改配置文件:
vim /etc/salt/master
file_roots:
base:
- /srv/salt
syndic_master: 172.25.13.4
3.设置完后重启master: systemctl restart salt-master.service
4.在server4(top-master)端安装master:
yum install -y salt-master
5.在server4上编辑配置文件:
vim /etc/salt/master
file_roots:
base:
- /srv/salt
order_masters: true
6.在server4上开启master:systemctl start salt-master.service
7. 在server1上开启syndic: systemctl start salt-syndic
8. 在server4(top master)与server1交换密钥

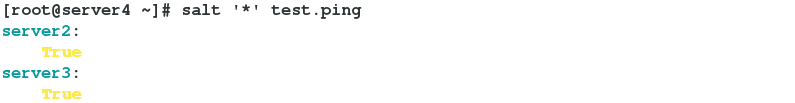
9. 测试:salt ‘*’ test.ping
三.salt-ssh模块
1.在server1上安装ssh:yum install -y salt-ssh
2.在server2和server3上将minion停止:systemctl stop salt-minion
3.在salt目录下: cd /etc/salt/编辑文件:
vim roster
server2:
host: 172.25.13.2
user: root
passwd: westos
server3:
host: 172.25.13.3
user: root
passwd: westos
4.测试:

四.API
1.在master端安装api:yum install -y salt-api
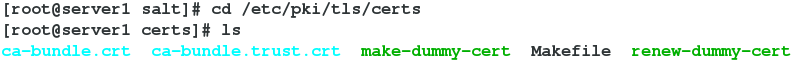
2. 进入到认证证书的目录:/etc/pki/tls/certs
在该目录下有一个Makefile文件,可以查看规则
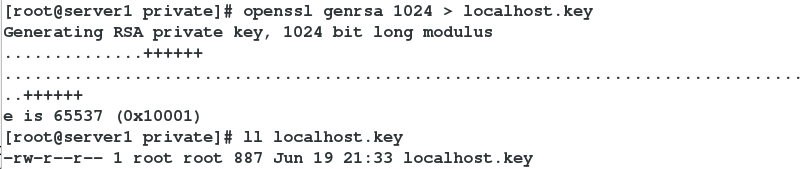
3. 进入到/etc/pki/tls/private/下
4. 生成key:openssl genrsa 1024
指定key的名字:openssl genrsa 1024 > localhost.key
查看是否生成:ll localhost.key

5. 进入到/etc/pki/tls/certs下进行认证

7.在/etc/salt/master.d/下创建文件api.conf
[root@server1 certs]# cd /etc/salt/master.d/
[root@server1 master.d]# vim api.conf
rest_cherrypy:
port: 8000
ssl_crt: /etc/pki/tls/certs/localhost.crt
ssl_key: /etc/pki/tls/private/localhost.key
8.编辑vim auth.conf
[root@server1 master.d]# vim auth.conf
external_auth:
pam:
saltapi:
- .*
- '@wheel'
- '@runner'
- '@jobs'
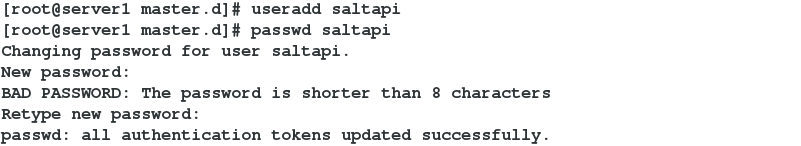
9.创建用户,并设置密码
10.重启master并开启api:
systemctl restart salt-master.service
systemctl start salt-api.service
11.查看8000端口是否打开:netstat -antlp

11. 在宿主机上测试:
curl -sSk https://172.25.13.1:8000/login -H 'Accept: application/x-yaml' -d username=saltapi -d password=westos -d eauth=pam

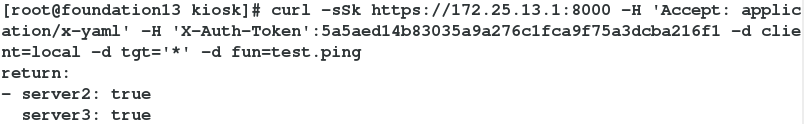
12. 通过token测试,此时要保证两个minion开启(server2和3上:systemctl start salt-minion):
curl -sSk https://172.25.13.1:8000 -H 'Accept: application/x-yaml' -H 'X-Auth-Token':5a5aed14b83035a9a276c1fca9f75a3dcba216f1 -d client=local -d tgt='*' -d fun=test.ping
14.在master(server1上)编辑文件:vim saltapi.py
# -*- coding: utf-8 -*-
import urllib2,urllib
import time
try:
import json
except ImportError:
import simplejson as json
class SaltAPI(object):
__token_id = ''
def __init__(self,url,username,password):
self.__url = url.rstrip('/')
self.__user = username
self.__password = password
def token_id(self):
''' user login and get token id '''
params = {'eauth': 'pam', 'username': self.__user, 'password': self.__password}
encode = urllib.urlencode(params)
obj = urllib.unquote(encode)
content = self.postRequest(obj,prefix='/login')
try:
self.__token_id = content['return'][0]['token']
except KeyError:
raise KeyError
def postRequest(self,obj,prefix='/'):
url = self.__url + prefix
headers = {'X-Auth-Token' : self.__token_id}
req = urllib2.Request(url, obj, headers)
opener = urllib2.urlopen(req)
content = json.loads(opener.read())
return content
def list_all_key(self):
params = {'client': 'wheel', 'fun': 'key.list_all'}
obj = urllib.urlencode(params)
self.token_id()
content = self.postRequest(obj)
minions = content['return'][0]['data']['return']['minions']
minions_pre = content['return'][0]['data']['return']['minions_pre']
return minions,minions_pre
def delete_key(self,node_name):
params = {'client': 'wheel', 'fun': 'key.delete', 'match': node_name}
obj = urllib.urlencode(params)
self.token_id()
content = self.postRequest(obj)
ret = content['return'][0]['data']['success']
return ret
def accept_key(self,node_name):
params = {'client': 'wheel', 'fun': 'key.accept', 'match': node_name}
obj = urllib.urlencode(params)
self.token_id()
content = self.postRequest(obj)
ret = content['return'][0]['data']['success']
return ret
def remote_noarg_execution(self,tgt,fun):
''' Execute commands without parameters '''
params = {'client': 'local', 'tgt': tgt, 'fun': fun}
obj = urllib.urlencode(params)
self.token_id()
content = self.postRequest(obj)
ret = content['return'][0][tgt]
return ret
def remote_execution(self,tgt,fun,arg):
''' Command execution with parameters '''
params = {'client': 'local', 'tgt': tgt, 'fun': fun, 'arg': arg}
obj = urllib.urlencode(params)
self.token_id()
content = self.postRequest(obj)
ret = content['return'][0][tgt]
return ret
def target_remote_execution(self,tgt,fun,arg):
''' Use targeting for remote execution '''
params = {'client': 'local', 'tgt': tgt, 'fun': fun, 'arg': arg, 'expr_form': 'nodegroup'}
obj = urllib.urlencode(params)
self.token_id()
content = self.postRequest(obj)
jid = content['return'][0]['jid']
return jid
def deploy(self,tgt,arg):
''' Module deployment '''
params = {'client': 'local', 'tgt': tgt, 'fun': 'state.sls', 'arg': arg}
obj = urllib.urlencode(params)
self.token_id()
content = self.postRequest(obj)
return content
def async_deploy(self,tgt,arg):
''' Asynchronously send a command to connected minions '''
params = {'client': 'local_async', 'tgt': tgt, 'fun': 'state.sls', 'arg': arg}
obj = urllib.urlencode(params)
self.token_id()
content = self.postRequest(obj)
jid = content['return'][0]['jid']
return jid
def target_deploy(self,tgt,arg):
''' Based on the node group forms deployment '''
params = {'client': 'local_async', 'tgt': tgt, 'fun': 'state.sls', 'arg': arg, 'expr_form': 'nodegroup'}
obj = urllib.urlencode(params)
self.token_id()
content = self.postRequest(obj)
jid = content['return'][0]['jid']
return jid
def main():
sapi = SaltAPI(url="https://172.25.13.1:8000",username="saltapi",password="westos")
#sapi.token_id()
print sapi.list_all_key()
#sapi.delete_key('test-01')
#sapi.accept_key('test-01')
#sapi.deploy('server3','nginx.serveice')
#print sapi.remote_noarg_execution('test-01','grains.items')
if __name__ == '__main__':
main()
14.运行测试:python saltapi.py

