The online security learning routes searched on major platforms are too rough. . . . can not watch anymore!
I took out the systematic learning route I organized and shared it with you! Click to view detailed roadmap
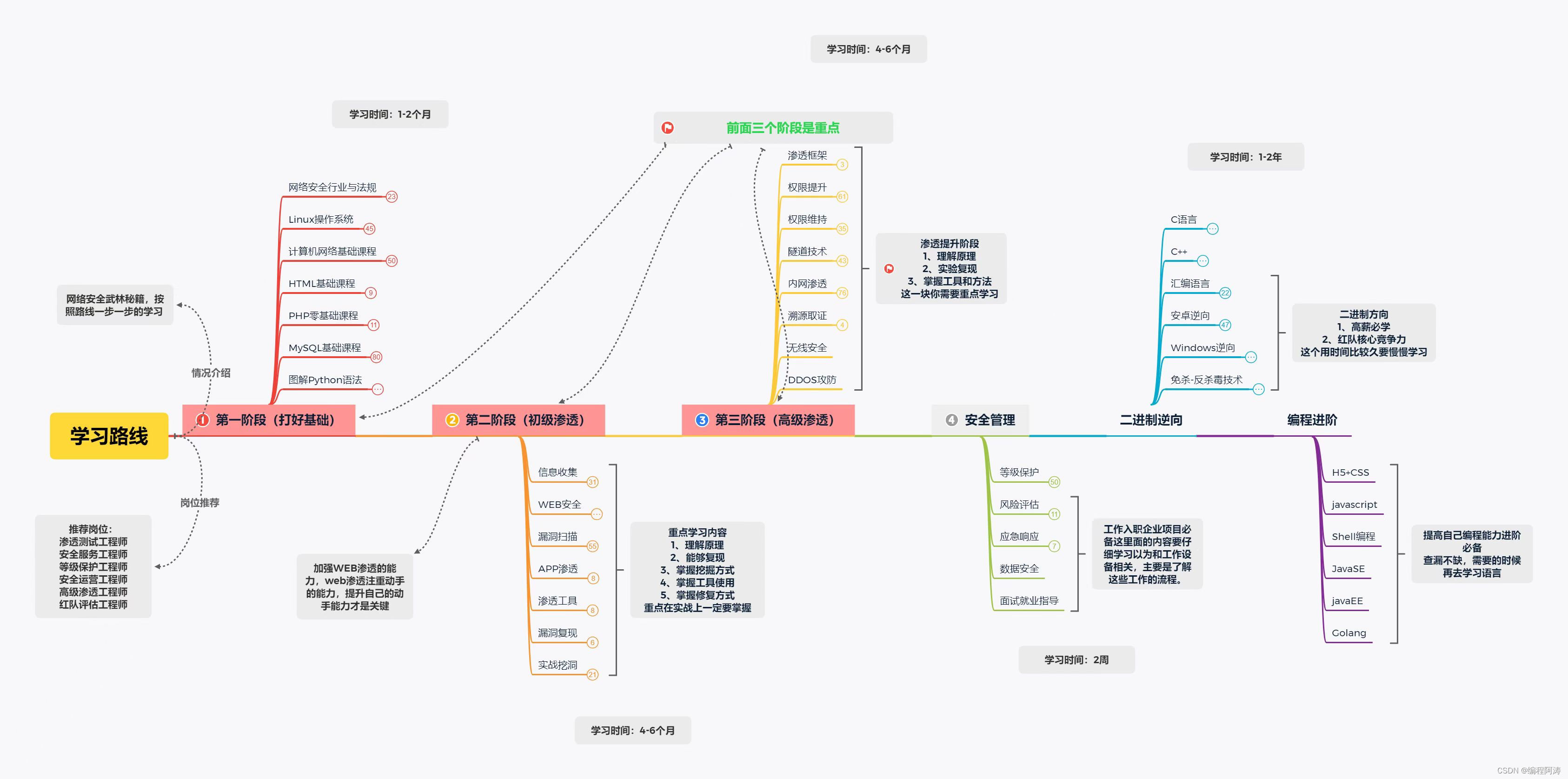
Suggested order of study:
1. Learning and popularizing the law on network security
1. Understand and introduce the "Network Security Law"
2. "Decision of the Standing Committee of the National People's Congress on Maintaining Internet Security"
3. "Regulations of the People's Republic of China on the Protection of
Computer Information 5. " Administrative
Measures for the Security Protection of International Networking of Computer Information Networks"
6. "Administrative Measures for Internet Information Services"
7. "Administrative Measures for Testing and Sales Licenses for Computer Information System Security Special Products"
8. "Communication "Network Security Protection Management Measures"
9. "National Security Law"
Other laws and regulations HTTPS://WWW.66LAW.CN/LAWS/415664.ASPX
2. Lay a solid foundation, sort out and review
Basics of LINUX system operation and maintenance
1, LINUX service management
2, Docker installation and use
3, LINUX security hardening
Network necessary foundation
1, physical layer
2, data link layer and switch
3, network model OSI TCP peer-to-peer transmission
4, virtual local area network VLAN
5, static routing and configuration
6, network address translation NAT
7, access control list ACL
8, IP protocol and IP address classification
9, subnet mask
10, gateway
11, subnet division
3. HTML and JAVASCRIPT (just understand the grammar, the requirements are not high)
1. Introduction to HTML? Why learn HTML
2. HTML document format, detailed explanation of entities
3. HTML tags, frames, tables, lists, forms, images, background explanations
4. Introduction to JAVASCRIPT
5. Features of JAVASCRIPT
6. Composition of JAVASCRIPT
7. How to Write JAVASCRIPT in the web page
4. Introduction to PHP
1. PHP environment construction, code writing tool selection
2. PHP basic grammar (function, variable, constant, comment, data type, flow control, arithmetic operation) 3.
PHP flow control (IF statement multiple nested SWITCH statement WHILE loop FOR Loop GOTO loop) PHP function
4, PHP regular expression
5, PHP file upload, PHP error handling
6, PHP operation MYSQL database
7, PHP session management and control
五、MYSQL/MSSQL
1. Database introduction, classification, installation, configuration, login, connection, etc.
2. Basic database operations Create, view, select, check database tables, delete databases and other related command line operations 3. Data
field operations create, modify, add, adjust field order, sort and delete 4. Database table operation
creation, viewing, selection, deletion of database tables and other related command line operations
5. Data type integer, floating point, character, time, matching type, etc.
6. Character set index
7. Addition, deletion, modification and query Update records, database permission operations
6. Key points
02 Hacking Rules
03 Industry Development and Employment Trends of Security Operation and Maintenance Engineers
04 Overview of enterprise-level website attack methods and common Linux systems. ..
05 Security Introduction / Virus / Malicious Program / Hacker / Intrusion /
06 CentOS7.The x template machine is packaged with system optimization / and attack and defense ring. ..
07 CentOS7.The x template machine is packaged with system optimization / and attack and defense ring. ..
08 Offensive and defensive environment construction / DVWA shooting range construction / website front-end technology. ..
09 Enterprise-level CentOS7. Common commands for x system directory management
10 Enterprise-level CentOS7. X system file operation basic commands
11Enterprise-level CentOS7. VI/VIM text editor in x system
12 Enterprise-level CentOS7. x system file permissions
13 Enterprise-level CentOS7. x system file attributes
14 Enterprise-level CentOS7. x system user management
15 Enterprise-level CentOS7. x system character set, wildcard, special. ..
16 Enterprise-level CentOS7. x system character set, wildcard, special. ..
17 Enterprise-level CentOS7. x file compression and file transfer (1)
18 Enterprise-level CentOS7. X system file search practical skills
19Enterprise-level CentOS7. x system timed task/scheduled task
20 Enterprise-level CentOS7. X system disk management and project combat
21 Enterprise-level CentOS7. x network management / and static routing project. ..
22 Introduction to Web Application Security and Risk for Penetration Testing
23 Web services such as Nginx/Apache/Tomcat for penetration testing. ..
24 Information collection of penetration testing security tools
25 Vulnerability Scanning of Penetration Testing Security Tools
26 SQL Injection Basics for Penetration Testing (Part 1)
27 Attack Framework of Penetration Testing Security Tools,
28 SQL injection basics of penetration testing (below), tools and POST. ..
29 Penetration testing asset sorting and Nmap tool introduction
30 SQL injection blind injection for penetration testing
31 SQL injection for penetration testing based on error injection (Part 1)
32 SQL injection for penetration testing based on error injection (Part 2)
33 SQL usage of SQL injection for penetration testing
34 SQL Injection for Penetration Testing and SQL Injection Defense, 35 Essential Tools for Penetration Testing (Part 1)
36 Essential Tools for Penetration Testing (Part 2)
37 Penetration Testing Vulnerability Mining / Vulnerability Scanning
38 Penetration Testing Kali Linux Security Penetration
39 levels of security protection process and penetration test report writing
40 Level Protection of Linux System Security Hardening (Part 1) 41 Introduction to Network Security Cross-site Scripting Attacks of Penetration Testing-XSS. ..
42 File Upload Vulnerability for Penetration Testing
43 Introduction to Network Security Cross-Site Scripting Attacks of Penetration Testing-XSS. ..
44 Introduction to Network Security Cross-Site Scripting Attacks of Penetration Testing-XSS. ..
45 Penetration Testing Network Security Service Request Forgery Vulnerability-CSRF
46 Penetration Test Network Security Service Request Forgery Vulnerability-SSRF, 47 Business Security Copper Leakage Top 10
48 Brute force cracking and verification code security of penetration testing
49 DDoS–DDoS, CC, SYN–Linux three major security attacks. ..
50 DDoS-Firewall Technology/Shell Programming Technology Practice
51 DDoS – DDoS Security Defense
52 DDoS-DDoS security defense
53 Security - Social Engineering (Part 1)
54 Security - Social Engineering (Part 2)
55 Access Denied Attack and Defense Description-DoS-DDoS, 56 Serialization and Deserialization
57 file upload
58 Social Engineering III
59 Social Engineering IV
60WAF Bypass Penetration and Defense
61 verification code security penetration and defense
62 WEBSHELL Related Penetration and Defense
63 system privilege escalation penetration and defense
64 database privilege escalation penetration and defense
65 Three-party application software security
66ARP Penetration and Defense
67 Intranet related penetration and defense
68 Wireless security-related penetration and defense
69 penetration report writing
70 Trojan Horse Avoidance Problems and Defenses
71windows security series problems
72 levels of protection
73 Risk assessment
74 safety inspection
75 emergency response
76 code audit
7. If you have spare time, you can study
1. ANDROID unpacking and reverse engineering
2. Shell in-depth
3. C in-depth learning
4. C++ in-depth learning
5. Go language
6. JAVA language
7. Windows unpacking and reverse engineering
8. Blockchain
9. CTF in-depth
super hacker
This part of the content is still relatively far away for students with zero foundation, so I won’t go into details, and attach the learning route.

If the picture is too large and compressed by the platform, it cannot be seen clearly.
After following me, the background will automatically send it to everyone! After paying attention, everyone can watch the background news!
Video supporting materials & domestic and foreign network security books, documents & tools

Of course, in addition to supporting videos, various documents, books, materials & tools have been sorted out for you, and they have been classified into categories for you.
Some video tutorials that the author bought by himself, but which are not available on other platforms for free.
SRC&Hacking Technical Documentation

If you want to get involved in hacking & network security, the author has prepared a copy for everyone: 282G the most complete network security data package on the entire network for free! After following me, it will be automatically sent to everyone! After everyone pays attention, just pay attention to the background news~
epilogue
Cybersecurity is a critical issue in today's society. With the rapid development of science and technology, the network has penetrated into every aspect of our lives, bringing us great convenience and opportunities. However, there are also various risks and threats in the network, such as hacker attacks, data leakage, etc. Therefore, learning network security knowledge has become a problem that everyone should pay attention to and pay attention to.
Special statement:
This tutorial is purely technical sharing! The purpose of this tutorial is in no way to provide and technical support for those with bad motives! Nor does it assume joint and several liability arising from the misuse of technology! The purpose of this tutorial is to maximize everyone's attention to network security and take corresponding security measures to reduce economic losses caused by network security. ! ! !