RE
1, easyre
dragged ida, get flag
2,helloworld
Apk file drag processing corrections, 
to give flag
3, xor
dragged ida, 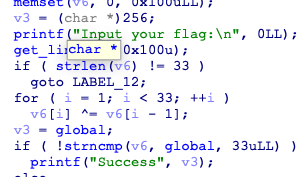
is a simple XOR, write scripts
glo=[0x66,0x0a,0x6b,0x0c,0x77,0x26,0x4f,0x2e,0x40,0x11,0x78,0x0d,0x5a,0x3b,0x55,0x11,0x70,0x19,0x46,0x1f,0x76,0x22,0x4d,0x23,0x44,0x0e,0x67,0x06,0x68,0x0f,0x47,0x32,0x4f]
x='f'
for i in range(1,len(glo)):
x+=chr(glo[i]^glo[i-1])
print(x)
Get flag
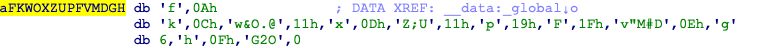
4, Happy New Year
exe dragged ida, found the shell, check shell 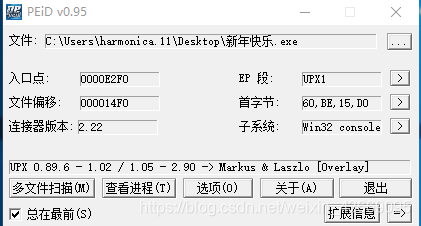
upx, with upx -d shelling, and then drag ida 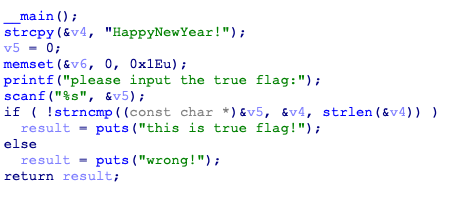
get flag
5, reserve1
EXE, dragged ida, there are a number of functions, so look at the string 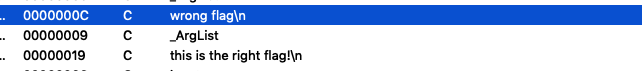
you see a suspicious string, the points go 
find a function call, and then point to go 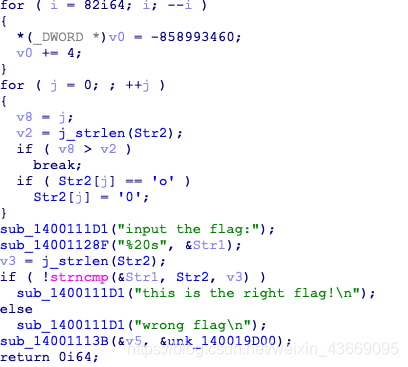
find the key function, analysis, string str2 in all o replace 0 is the flag
6,Mysterious
这题出在MISC里了,先找字符串
跟随
找到关键函数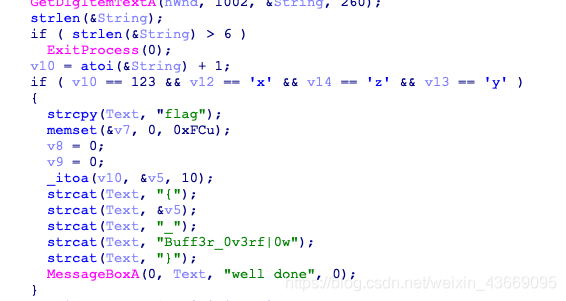
这里有个atoi()将字符串换为整形之后减一了,所以输入122xyz
得到flag
6,不一样的flag
许久未见的迷宫题,进main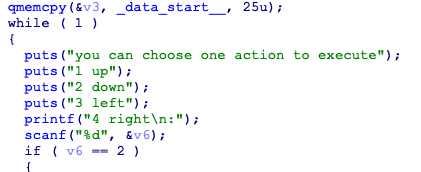
十分贴心的已经将上下左右分好了,然后看_data_start___这就是迷宫
由*开始,由#结束,每五个一换行
*1111
01000
01010
00010
1111#
走一遍的flag
7,SimpleRev
拖进ida,可以找到关键函数decry,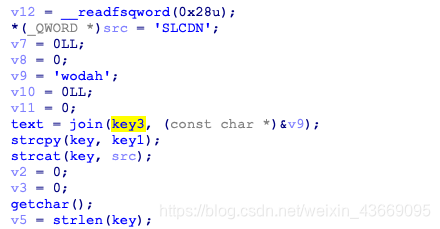
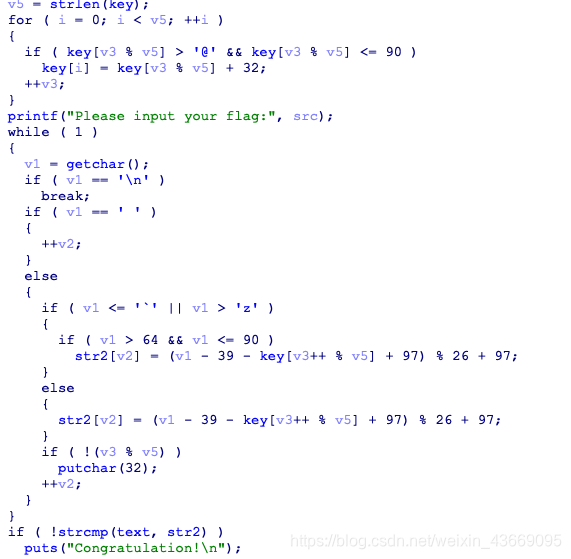
看key1,3,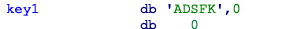
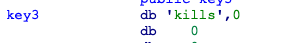
可以得到 text=killshadow,key=ADSFKNDCLS
然后程序对key进行了一番花里胡哨但其实就是把key变成小写的操作,于是得key=adsfkndcls,而我们要求的是v1,写脚本
#include<stdio.h>
int main(void)
{
char text[10]="killshadow";
char key[10]="adsfkndcls";
int v3=0;
int v5=10;
char flag[10];
for(int i=0;i<10;i++)
{
for(char j='A';j<='Z';j++){
char temp;
temp=(j-39-key[i]+97)%26+97;
if(temp==text[i])
flag[i]=j;
}
}
printf("%s",flag);
return 0;
}
Get flag
8, the connotation of software
attendance problems, dragged ida, get flag