12.17 Nginx负载均衡
Nginx负载均衡即为当代理服务器将自定义的域名解析到多个指定IP时,通过upstream来保证用户可以通过代理服务器正常访问各个IP。
负载均衡配置
配置参数:
[root@1 ~]# vim /usr/local/nginx/conf/vhost/load.conf
upstream aq.com
#自定义域名
{
ip_hash;
#保证同一个用户始终保持在同一台机器上
#即当域名指向多个IP时,保证每个用户始终解析到同一IP
server 61.135.157.156:80;
server 125.39.240.113:80;
#指定web服务器的IP
}
server
{
listen 80;
server_name www.qq.com;
location /
{
proxy_pass http://aq.com;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
}
}
检测
代理前
[root@1 ~]# curl -x127.0.0.1:80 www.qq.com
This is the default directory.
使用代理前,会直接解析到默认虚拟主机。
代理后
[root@1 ~]# /usr/local/nginx/sbin/nginx -t
nginx: the configuration file /usr/local/nginx/conf/nginx.conf syntax is ok
nginx: configuration file /usr/local/nginx/conf/nginx.conf test is successful
[root@1 ~]# /usr/local/nginx/sbin/nginx -s reload
[root@1 ~]# curl -x127.0.0.1:80 www.qq.com
使用代理后会解析到代理服务器所指向的IP
[root@1 ~]# dig www.qq.com
;; ANSWER SECTION:
www.qq.com. 138 IN A 61.135.157.156
www.qq.com. 138 IN A 125.39.240.113
;; Query time: 13 msec
;; SERVER: 119.29.29.29#53(119.29.29.29)
;; WHEN: 二 8月 15 16:41:11 CST 2017
;; MSG SIZE rcvd: 71
注意: Nginx不支持代理https,只能代理http,新版本的Nginx可以代理tcp。
dig命令
dig命令是常用域名解析工具。
如果服务器中没有该命令,手动安装:
[root@1 ~]# yum install -y bind-utils
语法: dig [域名]
http、https、tcp
HTTP超文本传输协议(HyperText Transfer Protocol)是互联网上应用最为广泛的一种网络协议。
HTTPS(全称:Hyper Text Transfer Protocol over Secure Socket Layer),是以安全为目标的HTTP通道,简单讲是HTTP的安全版。HTTPS协议是由SSL+HTTP协议构建的可进行加密传输、身份认证的网络协议要比http协议安全。
HTTP默认的端口号为80,HTTPS的端口号为443。
TCP(Transmission Control Protocol 传输控制协议)是一种面向连接的、可靠的、基于字节流的传输层通信协议,由IETF的RFC 793定义。默认监听80端口。
12.18 SSL原理
SSL(Secure Sockets Layer 安荃套接层)协议,及其继任者TLS(Transport Layer Security传输层安全)协议,是为网络通信提供安全及数据完整性的一种安全协议。
SSL工作流程
如果虚拟机中没有此工具,手动安装:
[root@1 ~]# yum install -y openssl
SSL工作流程
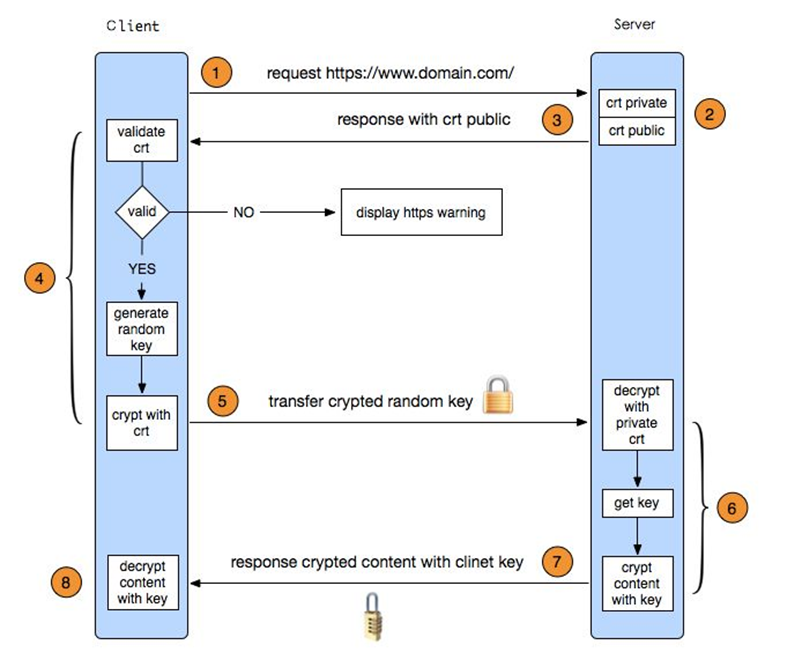
- 浏览器发送一个https的请求给服务器;
- 服务器要有一套数字证书,可以自己制作(后面的操作就是阿铭自己制作的证书),也可以向组织申请,区别就是自己颁发的证书需要客户端验证通过,才可以继续访问,而使用受信任的公司申请的证书则不会弹出>提示页面,这套证书其实就是一对公钥和私钥;
- 服务器会把公钥传输给客户端;
- 客户端(浏览器)收到公钥后,会验证其是否合法有效,无效会有警告提醒,有效则会生成一串随机数,并用收到的公钥加密;
- 客户端把加密后的随机字符串传输给服务器;
- 服务器收到加密随机字符串后,先用私钥解密(公钥加密,私钥解密),获取到这一串随机数后,再用这串随机字符串加密传输的数据(该加密为对称加密,所谓对称加密,就是将数据和私钥也就是这个随机字符串>通过某种算法混合在一起,这样除非知道私钥,否则无法获取数据内容);
- 服务器把加密后的数据传输给客户端;
- 客户端收到数据后,再用自己的私钥也就是那个随机字符串解密;
12.19 生成SSL密钥对
SSL证书就是一对公钥和私钥。
创建私钥
[root@1 ~]# cd /usr/local/nginx/conf/
[root@1 conf]# openssl genrsa -des3 -out tmp.key 2048
#生成SSL密钥
Generating RSA private key, 2048 bit long modulus
....................................................................................+++
...............................................................+++
e is 65537 (0x10001)
Enter pass phrase for tmp.key:
Verifying - Enter pass phrase for tmp.key:
说明: 在此指定密码!
转换key,取消密码:
[root@1 conf]# openssl rsa -in tmp.key -out adailinux.key
Enter pass phrase for tmp.key:
writing RSA key
删除密钥文件:
[root@1 conf]# rm -f tmp.key
生成证书请求文件
需要拿这个文件和私钥一起生产公钥文件:
[root@1 conf]# openssl req -new -key adailinux.key -out adailinux.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:adai
Locality Name (eg, city) [Default City]:Beijing
Organization Name (eg, company) [Default Company Ltd]:Beijing
Organizational Unit Name (eg, section) []:Beijing
Common Name (eg, your name or your server's hostname) []:adailinux
Email Address []:[email protected]
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:123456
An optional company name []:123456
说明: 该部分内容如果不购买证书可以自定义;如果是正式应用在网站上,需要规范填写对应信息(购买)。
创建公钥:
[root@1 conf]# openssl x509 -req -days 365 -in adailinux.csr -signkey adailinux.key -out adailinux.crt
Signature ok
subject=/C=CN/ST=adai/L=Beijing/O=Beijing/OU=Beijing/CN=adailinux/[email protected]
Getting Private key
12.20 Nginx配置SSL
[root@1 conf]# cd vhost/
[root@1 vhost]# vim ssl.conf
server
{
listen 443;
server_name adai.com;
index index.html index.php;
root /data/wwwroot/adai.com;
ssl on;
#开启ssl
ssl_certificate adailinux.crt;
#配置公钥
ssl_certificate_key adailinux.key;
#配置私钥
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
#配置协议
}
[root@1 vhost]# mkdir /data/wwwroot/adai.com
检测
报错:
[root@1 conf]# /usr/local/nginx/sbin/nginx -t
nginx: [emerg] unknown directive "ssl" in /usr/local/nginx/conf/vhost/ssl.conf:7
nginx: configuration file /usr/local/nginx/conf/nginx.conf test failed
未识别ssl配置,需要重新编译Nginx:
[root@1 conf]# cd /usr/local/src/nginx-1.12.1/
[root@1 nginx-1.12.1]# ./configure --prefix=/usr/local/nginx --with-http_ssl_module
[root@1 conf]# make
[root@1 conf]# make install
[root@1 nginx-1.12.1]# /usr/local/nginx/sbin/nginx -t
nginx: the configuration file /usr/local/nginx/conf/nginx.conf syntax is ok
nginx: configuration file /usr/local/nginx/conf/nginx.conf test is successful
[root@1 nginx-1.12.1]# /etc/init.d/nginx restart
Restarting nginx (via systemctl): [ 确定 ]
[root@1 nginx-1.12.1]# netstat -lntp
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN 5991/nginx: master
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 1735/sshd
tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN 2040/master
tcp 0 0 0.0.0.0:443 0.0.0.0:* LISTEN 5991/nginx: master
tcp6 0 0 :::3306 :::* LISTEN 1990/mysqld
tcp6 0 0 :::22 :::* LISTEN 1735/sshd
tcp6 0 0 ::1:25 :::* LISTEN 2040/master
nginx监听80和443端口。
测试
[root@1 nginx-1.12.1]# cd /data/wwwroot/adai.com/
[root@1 1.com]# vim index.html
This is ssl.
添加本地域名:
[root@1 adai.com]# vim /etc/hosts
127.0.0.1 adai.com
[root@1 vhost]# curl https://adai.com/
curl: (60) Peer's certificate issuer has been marked as not trusted by the user.
More details here: http://curl.haxx.se/docs/sslcerts.html
curl performs SSL certificate verification by default, using a "bundle"
of Certificate Authority (CA) public keys (CA certs). If the default
bundle file isn't adequate, you can specify an alternate file
using the --cacert option.
If this HTTPS server uses a certificate signed by a CA represented in
the bundle, the certificate verification probably failed due to a
problem with the certificate (it might be expired, or the name might
not match the domain name in the URL).
If you'd like to turn off curl's verification of the certificate, use
the -k (or --insecure) option.
因为该证书是自己创建的,所以提示证书不被信任!!!
注: 进行该测试之前需要更改Windows的hosts文件。