
注册了个账号然后登陆,这个颜色真的看得眼睛疼…浏览了下留言感觉好像都是比较正常的,试试简单的xss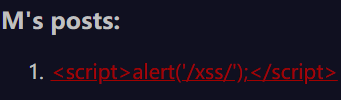 显然不行2333
显然不行2333
在post参数fuzz了一下,发现有路径穿越:

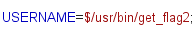
源代码中搜索发现: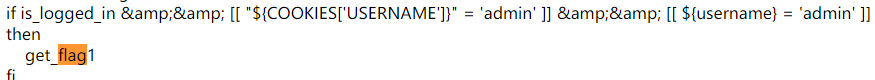
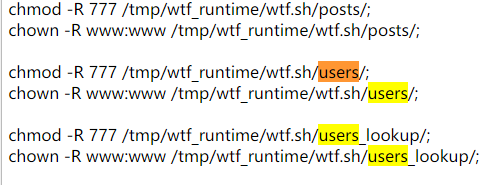
发现有名为users的文件夹,于是乎:

明显这里储存的是用户的TOKEN,抓包修改:

其中user参数很容易就得到了,这理解略过了,查看返回的代码,发现了flag

提交发现flag不对,定睛一看这才半段flag…
回到前面的…/开始快乐代码审计,先是找到这段代码:
max_page_include_depth=64
page_include_depth=0
function include_page {
# include_page <pathname>
local pathname=$1
local cmd=""
[[ "${pathname:(-4)}" = '.wtf' ]];
local can_execute=$?;
page_include_depth=$(($page_include_depth+1))
if [[ $page_include_depth -lt $max_page_include_depth ]]
then
local line;
while read -r line; do
# check if we're in a script line or not ($ at the beginning implies script line)
# also, our extension needs to be .wtf
[[ "$" = "${line:0:1}" && ${can_execute} = 0 ]];
is_script=$?;
# execute the line.
if [[ $is_script = 0 ]]
then
cmd+=$'\n'"${line#"$"}";
else
if [[ -n $cmd ]]
then
eval "$cmd" || log "Error during execution of ${cmd}";
cmd=""
fi
echo $line
fi
done < ${pathname}
else
echo "<p>Max include depth exceeded!<p>"
fi
}
发现服务器能执行wtf文件,接着代码审计555:
function reply {
local post_id=$1;
local username=$2;
local text=$3;
local hashed=$(hash_username "${username}");
curr_id=$(for d in posts/${post_id}/*; do basename $d; done | sort -n | tail -n 1);
next_reply_id=$(awk '{print $1+1}' <<< "${curr_id}");
next_file=(posts/${post_id}/${next_reply_id});
echo "${username}" > "${next_file}";
echo "RE: $(nth_line 2 < "posts/${post_id}/1")" >> "${next_file}";
echo "${text}" >> "${next_file}";
# add post this is in reply to to posts cache
echo "${post_id}/${next_reply_id}" >> "users_lookup/${hashed}/posts";
}
这是reply功能的代码,也是存在路径穿越的
我们可以使用户名为一段可执行代码,并且写入文件格式为wtf,就可以执行这段代码
先正常的回复一下,然后抓包进行修改,上传后门m.wtf,注意一点,m.wtf后面要加%09,表示制表符,否在会被当做目录去解析:

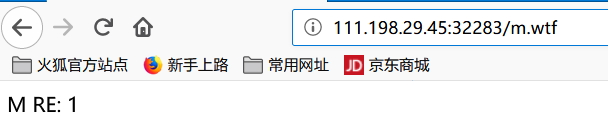
访问:
成功写入,接下来需要注册名称包含可执行代码的用户:

再注册一个:
重复上述步骤,访问m.wtf:
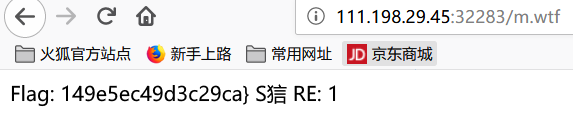
得到第二段flag
这题的代码审计太烦人呢,路径穿越这个点也不容易想到,脑洞怪大的…
