一.安装
项目地址:hashcat
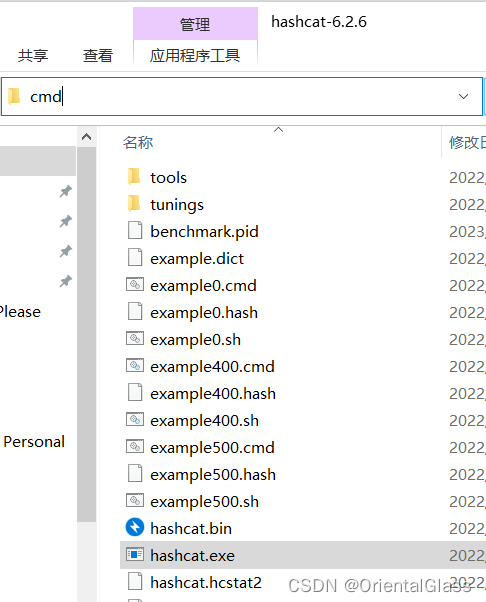
下载压缩包后解压,在所在文件夹中打开cmd即可
二.使用
- 基本参数
-m, —hash-type=NUM 哈希类别,其NUM值参考其帮助信息下面的哈希类别值,其值为数字。如果不指定m值则默认指md5,例如-m 1800是sha512 Linux加密。
-a, –attack-mode=NUM 攻击模式,其值参考后面对参数。“-a 0”字典攻击,“-a 1” 组合攻击;“-a 3”掩码攻击。
-V, —version 版本信息
-h, –help 帮助信息。
–quiet 安静的模式, 抑制输出
- 字符集
?l = abcdefghijklmnopqrstuvwxyz 代表小写字母
?u = ABCDEFGHIJKLMNOPQRSTUVWXYZ 代表大写字母
?d = 0123456789 代表数字
?s = !”#$%&’()*+,-./:;<=>?@[\]^_`{|}~ 代表特殊字符
?a = ?l?u?d?s 大小写数字及特殊字符的组合
?b = 0×00 – 0xff
- 攻击模式
0 = Straight (字典破解)
1 = Combination (组合破解)
2 = Toggle-Case (大小写转换)
3 = Brute-force(掩码暴力破解)
4 = Permutation(序列破解)
5 = Table-Lookup(查表破解)
6 = Hybrid dict + mask 字典加掩码破解
7 = Hybrid mask + dict 掩码+字典破解
8 = Prince(王子破解)
- 哈希类型
0 = MD5
10 = md5($pass.$salt)
20 = md5($salt.$pass)
30 = md5(unicode($pass).$salt)
40 = md5($salt.unicode($pass))
50 = HMAC-MD5 (key = $pass)
60 = HMAC-MD5 (key = $salt)
100 = SHA1
110 = sha1($pass.$salt)
120 = sha1($salt.$pass)
130 = sha1(unicode($pass).$salt)
140 = sha1($salt.unicode($pass))
150 = HMAC-SHA1 (key = $pass)
160 = HMAC-SHA1 (key = $salt)
200 = MySQL323
300 = MySQL4.1/MySQL5
400 = phpass, MD5(WordPress), MD5(phpBB3),MD5(Joomla)
500 = md5crypt, MD5(Unix), FreeBSD MD5,Cisco-IOS MD5
900 = MD4
1000 = NTLM
1100 = Domain Cached Credentials (DCC), MSCache
1400 = SHA256
1410 = sha256($pass.$salt)
1420 = sha256($salt.$pass)
1430 = sha256(unicode($pass).$salt)
1431 = base64(sha256(unicode($pass)))
1440 = sha256($salt.unicode($pass))
1450 = HMAC-SHA256 (key = $pass)
1460 = HMAC-SHA256 (key = $salt)
1600 = md5apr1, MD5(APR), Apache MD5
1700 = SHA512
1710 = sha512($pass.$salt)
1720 = sha512($salt.$pass)
1730 = sha512(unicode($pass).$salt)
1740 = sha512($salt.unicode($pass))
1750 = HMAC-SHA512 (key = $pass)
1760 = HMAC-SHA512 (key = $salt)
1800 = SHA-512(Unix)
2400 = Cisco-PIX MD5
2410 = Cisco-ASA MD5
2500 = WPA/WPA2
2600 = Double MD5
3200 = bcrypt, Blowfish(OpenBSD)
3300 = MD5(Sun)
3500 = md5(md5(md5($pass)))
3610 = md5(md5($salt).$pass)
3710 = md5($salt.md5($pass))
3720 = md5($pass.md5($salt))
3800 = md5($salt.$pass.$salt)
3910 = md5(md5($pass).md5($salt))
4010 = md5($salt.md5($salt.$pass))
4110 = md5($salt.md5($pass.$salt))
4210 = md5($username.0.$pass)
4300 = md5(strtoupper(md5($pass)))
4400 = md5(sha1($pass))
4500 = Double SHA1
4600 = sha1(sha1(sha1($pass)))
4700 = sha1(md5($pass))
4800 = MD5(Chap), iSCSI CHAP authentication
4900 = sha1($salt.$pass.$salt)
5000 = SHA-3(Keccak)
5100 = Half MD5
5200 = Password Safe SHA-256
5300 = IKE-PSK MD5
5400 = IKE-PSK SHA1
5500 = NetNTLMv1-VANILLA / NetNTLMv1-ESS
5600 = NetNTLMv2
5700 = Cisco-IOS SHA256
5800 = Android PIN
6300 = AIX {smd5}
6400 = AIX {ssha256}
6500 = AIX {ssha512}
6700 = AIX {ssha1}
6900 = GOST, GOST R 34.11-94
7000 = Fortigate (FortiOS)
7100 = OS X v10.8+
7200 = GRUB 2
7300 = IPMI2 RAKP HMAC-SHA1
7400 = sha256crypt, SHA256(Unix)
7900 = Drupal7
8400 = WBB3, Woltlab Burning Board 3
8900 = scrypt
9200 = Cisco $8$
9300 = Cisco $9$
9800 = Radmin2
10000 = Django (PBKDF2-SHA256)
10200 = Cram MD5
10300 = SAP CODVN H (PWDSALTEDHASH) iSSHA-1
11000 = PrestaShop
11100 = PostgreSQL Challenge-ResponseAuthentication (MD5)
11200 = MySQL Challenge-Response Authentication(SHA1)
11400 = SIP digest authentication (MD5)
99999 = Plaintext
特殊哈希类型
11 = Joomla < 2.5.18
12 = PostgreSQL
21 = osCommerce, xt:Commerce
23 = Skype
101 = nsldap, SHA-1(Base64), Netscape LDAPSHA
111 = nsldaps, SSHA-1(Base64), Netscape LDAPSSHA
112 = Oracle S: Type (Oracle 11+)
121 = SMF > v1.1
122 = OS X v10.4, v10.5, v10.6
123 = EPi
124 = Django (SHA-1)
131 = MSSQL(2000)
132 = MSSQL(2005)
133 = PeopleSoft
141 = EPiServer 6.x < v4
1421 = hMailServer
1441 = EPiServer 6.x > v4
1711 = SSHA-512(Base64), LDAP {SSHA512}
1722 = OS X v10.7
1731 = MSSQL(2012 & 2014)
2611 = vBulletin < v3.8.5
2612 = PHPS
2711 = vBulletin > v3.8.5
2811 = IPB2+, MyBB1.2+
3711 = Mediawiki B type
3721 = WebEdition CMS
7600 = Redmine Project Management Web App
三.爆破方式
- 掩码爆破
掩码爆破即已知一部分字符,需要爆破另一部分字符,或者已知字符类型,长度等信息暴力破解
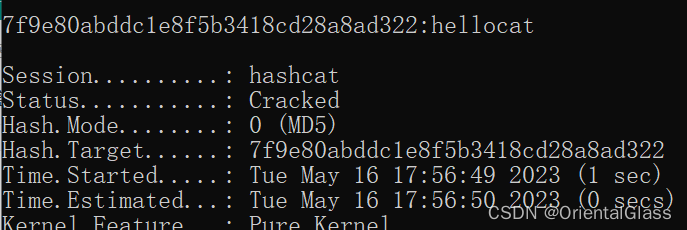
hashcat -m 0 -a 3 7f9e80abddc1e8f5b3418cd28a8ad322 ?l?l?l?l?l?l?l?l
成功爆破
- 自定义字符集
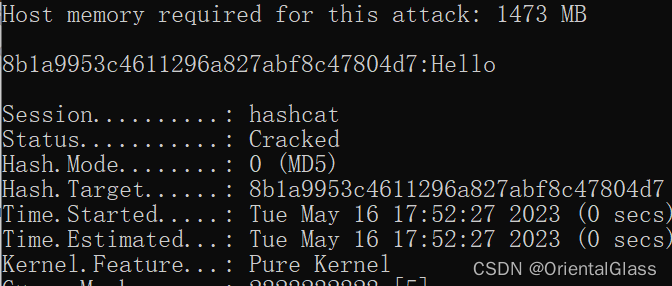
hashcat -m 0 -a 3 -2 ?u?l 8b1a9953c4611296a827abf8c47804d7 ?2?2?2?2?
成功爆破